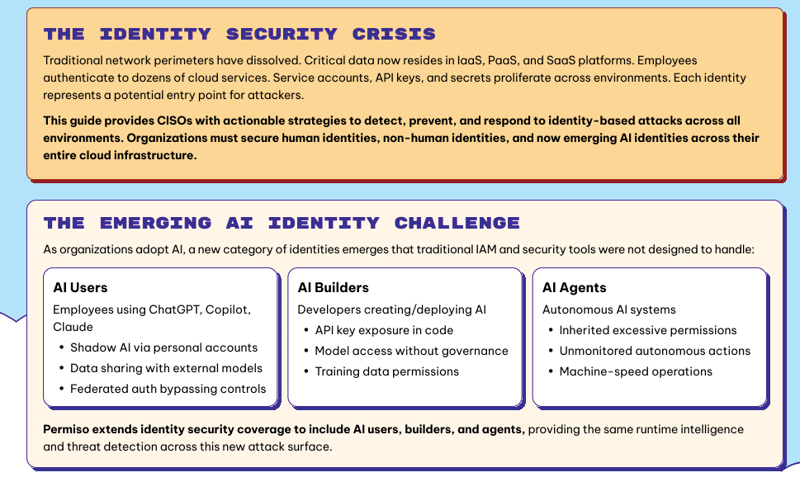
The CISO Guide to Identity Security
A Practical Playbook for Stopping Identity-Based Breaches Across Cloud, SaaS, and AI
90% of breaches now involve identity.
As organizations scale across IdP, IaaS, PaaS, and SaaS — and adopt AI — identity has become the primary attack surface. Human users, service accounts, API keys, OAuth tokens, vendors, and AI agents are creating visibility gaps that traditional tools can’t close.
This guide gives CISOs a clear, actionable framework to reduce identity risk, unify posture management and real-time detection, and secure human, non-human, and AI identities before attackers exploit them.
What You’ll Learn
- Why identity is now the #1 breach vector — and where traditional tools fall short
- How to unify ISPM + ITDR for full-spectrum identity visibility
- How to detect OAuth abuse, privilege escalation, and shadow AI in real time
- Quick-win priorities to reduce identity risk immediately
Get the Guide
trusted by these cool companies
Permiso has proven to be indispensable to the way we manage and secure identities across multiple environments
Permiso's ability to track identities and their activities across IaaS, SaaS and identity providers at runtime is unlike any of our existing solutions
Identity is the silver bullet in the cloud. If you don't get it right, you're dead!





