Securing AI Agents in the Enterprise
Five Identity-Driven Use Cases
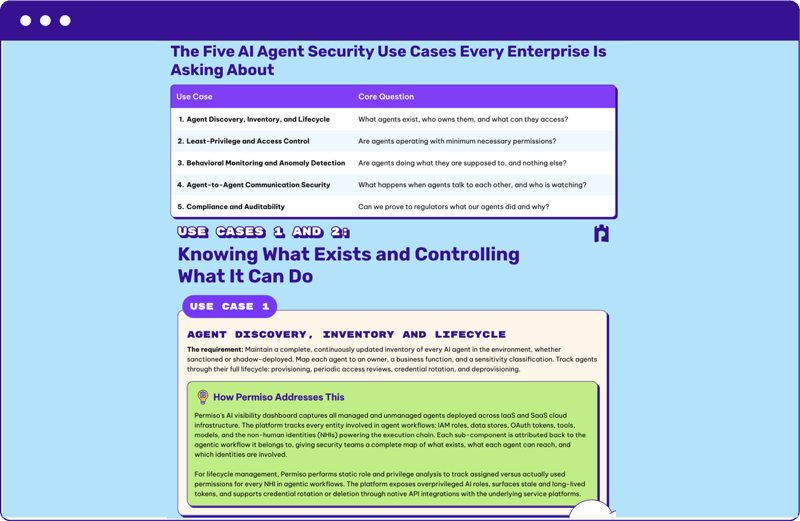
This guide breaks down the five AI agent security use cases that consistently surface in enterprise environments — and shows how Permiso solves them today.
At its core, AI agent security is an identity problem. Agents authenticate with credentials, operate through non-human identities (NHIs), inherit permissions, and act autonomously within your infrastructure. The attack surface isn’t the model — it’s the identity infrastructure that gives agents permission to act.
What You’ll Learn
- How to discover and inventory every AI agent: Gain continuous visibility into managed and unmanaged agents, map them to owners and business functions, and track their full lifecycle — from provisioning to credential rotation and deprovisioning.
- How to enforce least privilege for agents: Surface the gap between assigned and actually used permissions, detect overprivileged roles and stale tokens, and remediate credential risk before it becomes an attack path.
- How to monitor agent behavior in real time: Establish per-agent behavioral baselines, detect anomalous API calls and access patterns, and apply threat-informed detection to AI identities just as you do for human and non-human identities.
- How to secure agent-to-agent communication: Track token-based trust delegation across cloud boundaries, inspect inter-agent transactions, and optionally enforce inline blocking of malicious or policy-violating behavior.
- How to prove compliance and auditability: Map agent actions to governance frameworks like GDPR, HIPAA, ISO, and SOC 2, and produce regulator-ready audit trails that show which agent did what — and why.
Get the Guide
trusted by these cool companies
Permiso has proven to be indispensable to the way we manage and secure identities across multiple environments
Permiso's ability to track identities and their activities across IaaS, SaaS and identity providers at runtime is unlike any of our existing solutions
Identity is the silver bullet in the cloud. If you don't get it right, you're dead!





